
Context Engineering vs Prompt Engineering: What the Shift Means for Developers (2026)
Stop rewriting prompts. Learn when to use context engineering vs prompt engineering to optimize LLM context quality without complex RAG pipelines.
Read more about Context Engineering vs Prompt Engineering: What the Shift Means for Developers (2026)
Context Engineering for Developers: A Practical Guide (2026)
Master context engineering for developers. Learn the step-by-step workflow to assemble LLM context stacks, avoid context rot, and get better AI outputs.
Read more about Context Engineering for Developers: A Practical Guide (2026)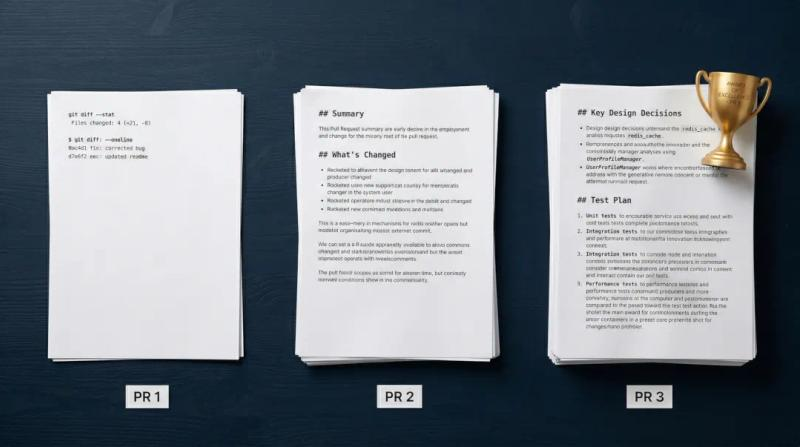
We Had Gemini Blind-Judge Three Claude-Generated Pull Requests. Here's the Template It Built.
We had Gemini blind-judge three Claude-generated pull requests. Here is the exact AI pull request template it built, and why rich code context is essential.
Read more about We Had Gemini Blind-Judge Three Claude-Generated Pull Requests. Here's the Template It Built.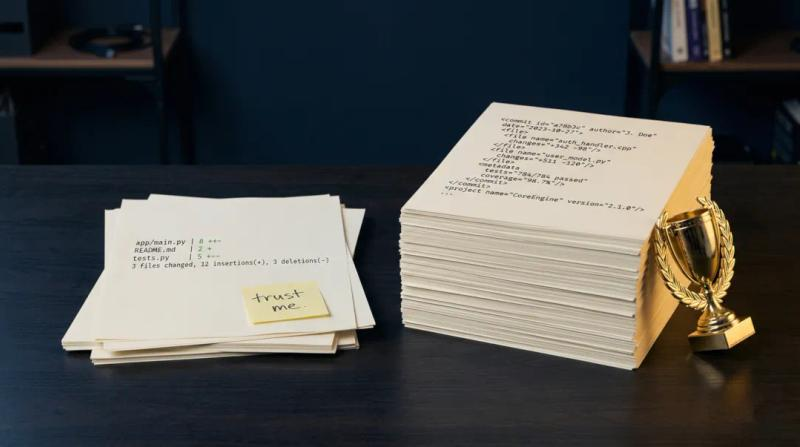
Claude Haiku 4.5 Outperformed Sonnet 4.6 on PR Writing - Context Was the Difference
Discover why Claude Haiku 4.5 outperformed Sonnet 4.6 in writing AI pull request descriptions. Learn why LLM context assembly matters more than the model tier.
Read more about Claude Haiku 4.5 Outperformed Sonnet 4.6 on PR Writing - Context Was the Difference